By encoding messages using the quantum states of photons, quantum cryptography offers the prospect of completely secure data transmission. However, physicists have found it difficult to make the single-photon sources needed in most variants of quantum cryptography. Now, Frédéric Grosshans of the Institute of Optics in Orsay, France, and colleagues have shown experimentally how to encode data using pulses containing several hundred photons. Their technique remains secure even when the pulses are degraded during transmission (F Grosshans et al. 2003 Nature 421 238).
In cryptography, the data in a message is encoded by multiplying it with a certain number. To decode the message the receiver must apply a second number, related to the first, called a key. But in order for cryptography to work, the key must be kept secret.
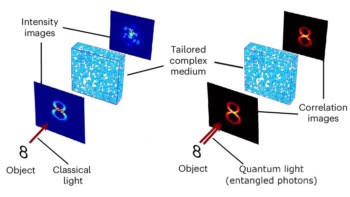
In most forms of quantum cryptography, the key consists of a sequence of single photons. To set the value of the key, the sender, known conventionally as Alice, chooses the polarization of each photon from among several non-orthogonal directions, and then transmits the photon. Quantum mechanics dictates that the polarization of a given photon is retained if the receiver, known as Bob, measures it in the same direction as Alice. But if Bob measures it in a different direction, he will only measure the correct value about half of the time.
To work out the key, Bob measures the polarization of each photon in whichever direction he chooses and telephones Alice to tell her which measurements he carried out. Alice then tells him which of the polarization values they agree upon — it is the photons with these values that are used as the secure key. By publicly comparing a portion of their key they will be able to confound an eavesdropper, known as Eve, since any measurement she makes on the key is likely to alter the values of some of the polarizations. Quantum mechanics also means that Eve is unable to make a perfect copy of the key and then pass it on to Bob.
In their system, Grosshans and co-workers use the average values of the amplitude and phase of the electric field of a group of photons, rather than the polarization of individual photons. Like the polarization of an individual photon, these variables are constrained by the uncertainty principle. But unlike the polarization of an individual photon, which can only assume one of two values along each orthogonal direction, these variables can assume a continuous range of values.
Several groups are investigating such continuous variables for use in quantum cryptography, but Grosshans and co-workers are the first to demonstrate their potential experimentally, as well as carrying out the hardware and software steps needed for manipulation of the secret key. Because their system measures continuous variables, it does not depend on being able to measure every single photon that is transmitted. In fact the researchers were able to securely send 75, 000 key bits per second, even though over half of the transmitted signal was lost.
“Our scheme is potentially much faster than single photon counting,” says Philippe Grangier, leader of the group. “This makes it suitable for high secret bit rates over short distances – typically less than 15 km – but its behaviour over longer distances requires further analysis.”
The researchers’ next step is to build a demonstration device that can transmit photons along optical fibres.