A straightforward and effective way for eavesdroppers to copy secret keys from quantum cryptographic systems has been tested by physicists in Germany. The technique does not require intercepting the quantum code itself, but merely sending a series of well timed weak light pulses to blind the receiver’s detectors and then listening to a public, unencrypted message between sender and receiver. The researchers, however, have also put forward a relatively simple way to counter the loophole.
The hacked system involves the sender (Alice) encrypting a confidential message using a key that she shares with the receiver (Bob). The key is encoded using the polarization states of a series of single photons, with each photon polarized in one of four ways – horizontally, vertically or in one of two diagonal directions. In theory the scheme is secure against eavesdropping attacks by a third party called Eve because any attempt to copy the key while en route from Alice to Bob – who has one detector for each polarization – will be exposed by the effect it has on Bob’s measurements.
This approach is used in a number of commercial encryption devices, and has been used in a limited number of financial and administrative transactions. However, while uncrackable in principle, it has been shown by various research groups to be vulnerable in practice, particularly because of limitations of Bob’s single-photon detectors. Last month, for example, Christian Kurtsiefer of the National University of Singapore and colleagues used bright light to “blind” the avalanche photodiodes within the detectors, allowing them to manipulate Bob’s measurements and steal the key without revealing their presence.
“Dead time” interception
Like a number of other eavesdropping techniques, the one developed by Kurtsiefer’s group involves intercepting the key sent by Alice and then resending it on to Bob, which is quite a complex operation. However, the new research, carried out by Henning Weier of Ludwig Maximilians University in Munich and colleagues and the firm qutools, does not require such an interception. This is because it exploits avalanche photodiodes’ “dead time” – the time it takes to recharge a photodiode once it has detected a photon, or the minimum time between two successive single-photon measurements, which is generally at least 50 nanoseconds.
The idea is that Eve injects a pulse of light, polarized in any one of the four directions measured by Bob, into the communication channel shortly before Alice sends each of her single photons. Above a certain minimum intensity, each pulse should trigger three of Bob’s detectors – those corresponding to the polarization assigned by Eve and the two, non-orthogonal states. If the delay between each pulse and single photon is much less than the photodiodes’ dead time, these three detectors will be unable to detect Alice’s photons.
This leaves only the orthogonal detector free to make detections. This means that Bob will only detect the photons sent by Alice that have a polarization which happens to be at right angles to that chosen by Eve for the corresponding pulse. When Bob then tells Alice over an open channel which photons he has detected, Eve simply notes the polarization of the corresponding pulses and the resulting sequence of orthogonal polarizations is equal to the secret key.
Less than 18 photons needed
To test the scheme, the team set up standard Alice and Bob instruments in the lab, communicating through about 1 m of free space. Eve was a second transmitter that was timed to send pulses 200 ns ahead of each photon from Alice. This is within the deadtime of 500 ns. By inserting appropriate filters in front of Eve, the researchers found that, as expected, the match between Eve’s stolen key and that recorded by Bob improved as the intensity of the blinding pulses increased. However, the minimum intensity needed to create a good match was not very high.
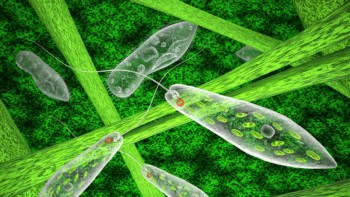
In fact, containing an average of just 16.5 photons provided Eve with a key that had a 98.8% overlap with that of Bob. As illustrated in the figure above, the high overlap provided a pretty accurate decryption of an image of the emblem of the University of Munich.
The researchers have also proposed a simple countermeasure to their hacking scheme. The solution, according to Weier, is to ensure that all four of Bob’s detectors are continuously active and able to respond to a single photon. This, he says, can be done by adding “just a bit more electronics”.
“Simple and elegant”
Vadim Makarov, a member of Kurtsiefer’s group, describes the Munich hacking technique as “simple and elegant”. But he points out that it does have a weakness – by blocking off three out of every four photons that Bob should receive it reduces the bit rate to one quarter of its normal value. “It may be difficult for Eve to trick Alice and Bob into believing the reduced bit rate is normal,” he added.
Makarov also points out that commercial quantum key distribution systems manufactured by ID Quantique and MagiQ Technologies are immune to this kind of attack. But he says that many research systems are vulnerable. “It is very useful that this paper is published and everybody can see how to design their systems properly,” he added.
The research is published in New Journal of Physics 13 073024.