Researchers in the UK and Germany have used quantum entanglement to securely distribute secret keys among multiple users in a network. By distributing entangled photons over optical fibres at telecommunications wavelengths, the team demonstrated that conventional telecoms infrastructure offers a viable path towards realizing a large-scale network of interconnected quantum devices – and perhaps even quantum-secure conference calls using Zoom or other platforms.
To send messages securely, two or more parties must first share, or exchange, a secret key, which is a string of genuinely random bits used to encrypt and decrypt messages. Quantum key distribution (QKD) protocols such as the widely-known BB84 protocol have previously been used to perform this key exchange between two users.
In the original BB84 protocol, a user wishing to securely send a bit to another would encode their secret bit onto a quantum state and transmit the quantum state via public, unsecure channels. A fundamental tenet of quantum mechanics, the no-cloning theorem, guarantees that a third party cannot silently eavesdrop on such a communication without revealing their presence. In subsequent versions of BB84, the two communicating parties share several entangled pairs of qubits and make random measurements on their respective qubit to derive a secret key.
Conference key agreement
In multi-user communications, it is often desirable for all parties to share a single secret key, such that each member can decrypt messages broadcast by any other member of the group. The process by which users of such a network share a key is called conference key agreement (CKA). According to Joseph Ho, one of the authors of the paper, this type of multi-user key distribution can provide strong encryption for tasks such as video conference calls.
In principle, it is possible to use two-party protocols like BB84 to share N-1 key pairs between N users and use classical methods to distil the conference key. In this technique, a designated leader in a network establishes N-1 secret keys with each other member and then transmits the conference key to each member, encrypting it with their respective secret key. However, this method is inefficient and will be impractical in future quantum networks that need to host many users.
Distributing entanglement across a distance
A more efficient alternative is to derive the key from multipartite entanglement. In this method, a multipartite entangled state is distributed to all members and each member performs measurements on their own qubits to generate the key.
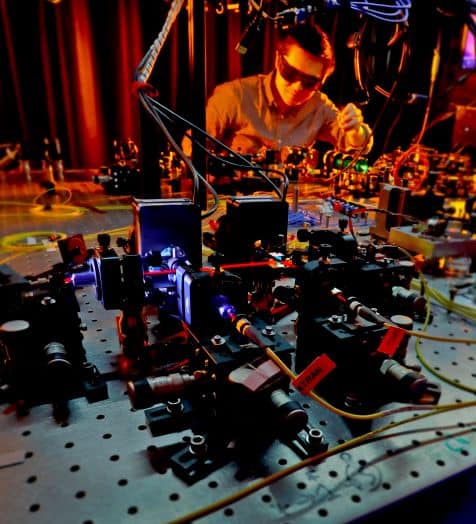
In their experimental demonstration, Ho and Massimiliano Proietti, working in a group led by Alessandro Fedrizzi of the Institute of Photonics and Quantum Sciences at Heriot-Watt University in Edinburgh and together with colleagues from Heinrich-Heine-Universität Düsseldorf in Düsseldorf, used a multi-user QKD protocol to securely exchange data in a network consisting of four parties. At the core of their experiment are quantum states that contain four photons in an equal superposition of two states: one where they are all horizontally polarized, and another where they are all vertically polarized. Copies of these four-photon states, which are known as Greenberger-Horne-Zeilinger (GHZ) states, were distributed to four members in a network, separated by up to 50 kilometres of optical fibre. The researchers also use additional techniques to correct any errors in distribution of the key, followed by a round of privacy amplification to further enhance the scheme’s security.
Quantum cryptography network spans 4600 km in China
During the experiment, which lasted 177 hours, the team generated a secure key containing over a million bits. The key was then used to securely share an image between four users in the network.
The fact that the experiment was conducted using conventional optical fibre at standard telecommunication wavelength indicates that existing communication infrastructure can be used for quantum-assisted key distribution. However, according to the researchers, much remains to be accomplished before CKA schemes such as the one implemented at Edinburgh can be reliably used for secure communication outside the laboratory. “One of our general goals is to demonstrate our CKA scheme in a field-test,” Ho tells Physics World.
For that to happen, researchers will first need to develop new capabilities for creating large entangled states at an appreciable rate and distributing them over long distances.
The research is published in Science Advances.



