Safeguarding our communications data and infrastructures will become a much harder task in a quantum-enabled future. KETS Quantum Security chief executive Chris Erven talks to Tushna Commissariat about how integrating quantum-based systems into existing communication is key

Academics, governments and the technology industry are all involved in a global race to build the first usable and scalable quantum computer. And when that goal is achieved – most likely within the next five to 15 years – we will not only have unprecedented computing power at our disposal, but also the worrying issue of safety. That’s because such a device could easily be used to hack into our current public-key cryptography, which underlies almost all of our digital transactions and interactions today. With this in mind, KETS Quantum Security – a UK firm – has been working on securing communications in the “post-quantum” world, according to its chief executive Chris Erven.
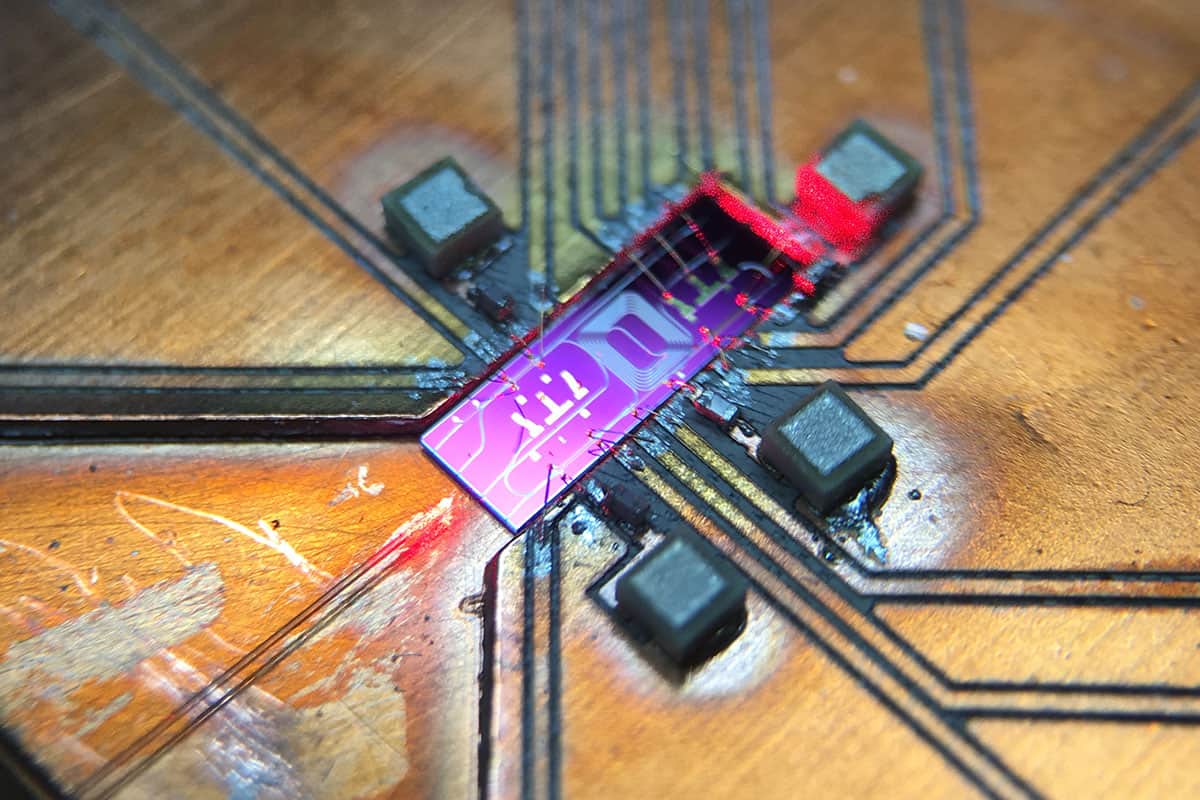
The Bristol-based company has spent the last decade developing a fast and powerful chip-based quantum random number generator, as well as full quantum key distribution (QKD) devices. Erven – who was deputy director of the Quantum Technology Enterprise Centre at the University of Bristol – has long been interested in the commercial application of quantum encryption. Here he talks to Physics World about the real-world security issues that all organizations may soon face and explains how KETS is currently working with a number of blue-chip organizations in sectors that range from telecommunications and defence, to data and finance. Erven also reveals his vision of our quantum future.
What are the key challenges, focuses and aims of the quantum-cryptography industry today?
It is fair to say that the industry, which has been around for a while now, is maturing. No one would deny that China leapt ahead when it comes to QKD and really moved the field along. They launched the Micius satellite, which established an ultrasecure link between two ground stations separated by more than 1120 km. And as of this year they have built a QKD network spanning thousands of kilometres and linking four main metropolitan areas in the country. These advances made a number of other governments sit up and pay attention.
Outside of China, the next biggest project is the European Quantum Communication Infrastructure (EuroQCI) Initiative, which involves developing a quantum-safe communications network that spans all 27 member states of the European Union (EU), and aims to be fully operational by 2027. It’s an interesting beast as it has a centralized plan, as well as projects in individual countries – for example, we are working with the Paris QCI. Here in the UK, too, the government is talking about “preparing for quantum-safe cryptography”. And of course the US has a number of initiatives – in fact the US Department of Energy has put considerable emphasis and funding into this. So a lot has flowed from all this government interest – it has provided new opportunities for vendors to sell kit into test beds.
When it comes to the technology of quantum security, it’s early days still and we are only at the bulletin-board stage. Yes, we have the internet, but it’s a bit unreasonable to assume that we’re going to jump right to the quantum internet – although many people are starting to get their heads around that. At KETS today we are part of some ongoing test beds in Europe and Canada which serve multiple purposes – that way, an end-user doesn’t have to pay ridiculous sums to do it all in-house, they can join a test bed. And technology providers can see how users plan on using these systems and improve on them.
When it comes to the quantum-computing race, the final stages have really begun, and that is raising awareness. Quantum computing is coming up more and more in our feeds and people are realizing that there’s plenty of good things, but there’s also some stuff that you’ve got to think about the implications for, one of them being security. So that has changed the conversation from “We should keep an eye on that” to suddenly a lot of private and public institutions thinking seriously about their security, which is great for us.
What are some of your goals and targets at KETS in the next couple of years, technology-wise?
Our latest £3.1m pre-series A funding round was announced in June this year. We continue to enjoy incredible support from our bedrock investor, Quantonation, who has been with us since seed, and were really lucky to add two new, great investors in SpeedInvest and Mustard Seed MAZE. The pandemic has slowed everybody down, but our main aim is to get our two products – a quantum random number generator (QRNG) and a QKD system – ready for users. The QRNG has been built and is ready. The QKD system should be ready any day now, when one of our team finds that last line of code where the bug is! So we’re within a hair of the second one.
The new funding will be used to accelerate development, production and delivery of the first products. It will also allow KETS to expand key first trials of the technology in real-world applications and environments that are already in development. To deliver all of this, KETS will continue to build a world-leading team that is passionate about the company’s technology and values.

The rest of our funding will be to build a few of them and trial the QRNG and the QKD system – we’ve talked to a number of people now in telecoms, in data centres and in defence and space; and will be testing some proof of concepts. So the next year is going to be testing as much as we can and bringing in users. We will be taking the early versions of our kits to people in a number of sectors, doing demos and then looking at the next steps to show off our technology. And then we want to start running as fast as possible, to go from there to 10 units to 10,000 units, and to make sure that we’re involved in key projects such as the EuroQCI.
Lastly, we have a few things in the pipeline that bring new capabilities that we would like to accelerate. This includes multi-transceiver devices, rather than just point-to-point, because that is looking closer to the internet and not the bulletin-board systems of the 1990s. So next year is all about demos and proof of concepts, and the year after that the plan is to build 10,000 of them and bring the next capabilities online.
Tell me a bit more about your QRNG and QKD systems, and who you think your key users will be
Our QRNG does exactly what it says on the tin – it produces random numbers according to the laws of physics. It sounds incredibly boring, but every past, present and future encryption algorithm needs good randomness. And then we have our QKD system that would let you and me exchange a symmetric key. So it’s a random sequence of zeros and ones, but only you and I know it, and distributing the key is now secure according to the laws of physics.
We call both of these our “development kits”. The cyber industry is an interesting one – as much as I try to show up to new customers and say, “Right, tell me all the ways you’re insecure so I can help,” they generally aren’t so forthcoming. It takes a while to build trust and get users to open up a little bit. Most of them just want to either get involved in a trial or to have us come and do a demo – some sort of three-month proof of concept, which ultimately helps build momentum at their end too.
This is also practical, as there are no established standards yet for quantum-security technologies or post-quantum algorithms – they’re still being written. There are some drafts in place, and it might meet some basic criteria, but in the sense of putting a sticker on the box saying “quantum safe” – it’s just not certified. So development kits in the hands of users will help us get there as they will contribute to writing the basic standards. With this in mind, we are focused on the telecommunications industry, as it’s a necessary first step. There’s definitely good sales there, both because they want to resell on these services, but they’re also a customer as they’re thinking about upgrading their own infrastructure to make it quantum-safe. A bank is not going to put in a fibre network between all of its locations, it’s going to turn around to BT and say, “I’d like to connect around the country.”
So you start with the telecoms to get the basic infrastructure and then you begin hanging use-cases off it. And we think one of the first big ones is data centres, because that’s where a lot of high-value data is being stored, processed and accessed. We hope to start with making some of these high-value links secure because there’s still a high cost of the technology.
We have also always worked with the defence and space industries, who obviously want good security, and have done things like put our test kits on Airbus unmanned aerial vehicles and fly them around. And of course, there is banking, finance and critical infrastructure – anything from ferrying around “no fly” lists and passport information between home office and airports, to securing next-generation nuclear power plants. In recent times, we’ve seen a number of hacks on energy grids and the like, so all these areas must be made secure.
From your point of view, what kind of timeline are you planning for when it comes to having a functional quantum computer?
We have some materials that we tend to send to customers now, that have been written by third-party experts such as quantum scientist Michele Mosca, working with the Global Risk Institute, who surveyed the field. Their estimate is a one in seven chance within five years and a one in two chance within 10 years.
The other key factor is all the investment going into quantum computing, which has really taken off in the last couple years – so we’re trying to put our money where our mouth is. Quantum computers are such a key resource, and in many cases they are now being developed by state actors in the US, China and the EU. You probably won’t know when the first one’s turned on. So we’ll probably never actually know when “Q day” is, unless it’s 50 years later, like with the Enigma machine where we found out much later. It could already have happened! I don’t think that’s quite the case just yet, but I think it’s closer than we think. So we plan for five-ish years.
We have a small, internal project looking at how we would make KETS quantum-safe – because currently we don’t have the full infrastructure to, say, access our Google docs in a quantum-safe way, and we’re a company of 14 at the moment. But even in a small start-up, it’s a can of worms when you open it up and consider all the ways you communicate and all the places your data goes. I can only imagine what it’s like for a multinational company. So even if Q day is 10 to 15 years away, it’s probably a 20 to 25 year transition for large companies, so they really should be looking into it.
Quantum cryptography goes faster and further on commercial fibre links
Tell me more about your quantum random number generator and why it’s such an important resource?
There are a number of QRNGs on the market – for example, ID Quantique has a chip focused on IoT [internet of things] smart devices and applications that perform at slower speeds. Ours focuses on high speed, as it is aimed towards data centres and telecommunications, who will gobble up as much randomness as you can give them. Today, our development kit is similar to a graphics-card chip, but we are going to continue to shrink it. It currently goes up to a gigabit per second; but natively it can do up to seven gigabits per second of randomness. We think we can push it to 25 without changing much, beyond some of the electronics.
The challenge has always been for anybody that doesn’t have quantum engineers on staff. They would ideally love to have a number in mind, so that they can say “this is 40 times better than my classical random number generator”, and an executive can then sign off on spending resources for that – but it’s just fundamentally different. So, early days this has been a challenge. Something that’s really helping that argument is developing a few more certification efforts or security assurance efforts. We are part of an Innovate UK project called AQuRand that has brought together a bunch of QRNG vendors and the National Physical Laboratory (NPL) is putting them through their paces. NPL is testing all the components and evaluating whether the model the company says this operates by actually holds true – and this will go a long way towards assuring users.

Data centres are certainly a big user because I don’t know any server that won’t spin up a hundred or a thousand virtual machines on any given day, and all those get populated with current cryptographic keys. So not even thinking about the “post quantum” future – they need thousands of keys today and the best-quality randomness.
Looking ahead to post-quantum algorithms versus QKD, you will still need good randomness. KETS has partnered with French startup CryptoNext to carry out some demonstrations. We injected our randomness into their post-quantum algorithms and they injected that into a popular open-source library. We then did a quantum-safe digital document signing demo by the end of the day. So we’re really trying to show every possible application of our technology.
Where might you use a post-quantum algorithm over quantum security tech, and vice versa?
At KETS, we produce quantum-security hardware. But there’s also post-quantum cryptography algorithms, which are updates to the software algorithms we currently use for security. To the best of our knowledge, they are secure against a quantum computer – it’s never been proven but there is ample evidence. And so, it comes down to the use case – if it’s financial high-frequency trading, then you care for a millisecond that the algorithm is good enough. But if you care about your medical records or your genome being stored over a lifetime, with data being exchanged back and forth between sites, then you care for a much longer period of time, and a layered approach to security is necessary.
Where is quantum computing headed, in the near term?
The key challenges for quantum computing are the ability to scale-up our small quantum computers, and to perform quantum error corrections. Companies are looking at different ways to do this: they’re designing novel qubits and control hardware. Quantum software firms are building quantum operating systems, but also beginning to try and optimize errors and get rid of them with machine learning at more of a firmware level. No one has won yet in terms of which technology you should build your quantum computer from, but I don’t think we’re far away from some exciting breakthroughs! Before we know it, I’ll be playing quantum solitaire on my quantum computer thinking nothing of what’s under the hood, just like we no longer marvel at the smartphones in our pockets.